safety assessment
Status of industry
In recent years, under the backdrop of increasingly severe information security situations both at home and abroad, threats from lawless individuals driven by interests and even hostile hacker organizations from abroad have become increasingly prominent. Network attack techniques have been constantly innovated, and incidents such as asset theft and data leakage caused by vulnerabilities in important information systems of units have occurred frequently.
The users of government, finance, enterprises and other industries are numerous, and the systems and applications are complex. Especially for systems involving user privacy data and transaction functions, their protection has brought unprecedented challenges to the daily security operation of each unit. How to ensure the business continuity of relevant information systems and resist various external threats, and establish a complete information security guarantee system, has become a key issue that each unit urgently needs to solve at present.
Solution
(1) Comprehensive asset mapping across the entire network
- Internet asset mapping
The prerequisite for an effective security assessment is to have a comprehensive understanding of the security status of the relevant units, especially the unexplored assets that have remained unknown for a long time. These assets are exposed to the Internet due to certain specific factors, such as in search engines, DNS resolution records, etc. If not dealt with, they are very likely to become attack platforms exploited by attackers for lateral or in-depth penetration of important target systems. By using the comprehensive asset mapping system, the exposed Internet assets can be quickly mapped and output through the unit name, combined with security big data and relevant unit certificates, IPs, domain names, fingerprints, keywords, etc., to generate an Internet exposed asset report.
- Internal Network Asset Detection
On the other side of the Internet assets, there exists a vast information asset system within each unit's network, including various network devices, servers, storage, databases, virtual machines, applications, security equipment, test hosts, office terminals, etc.
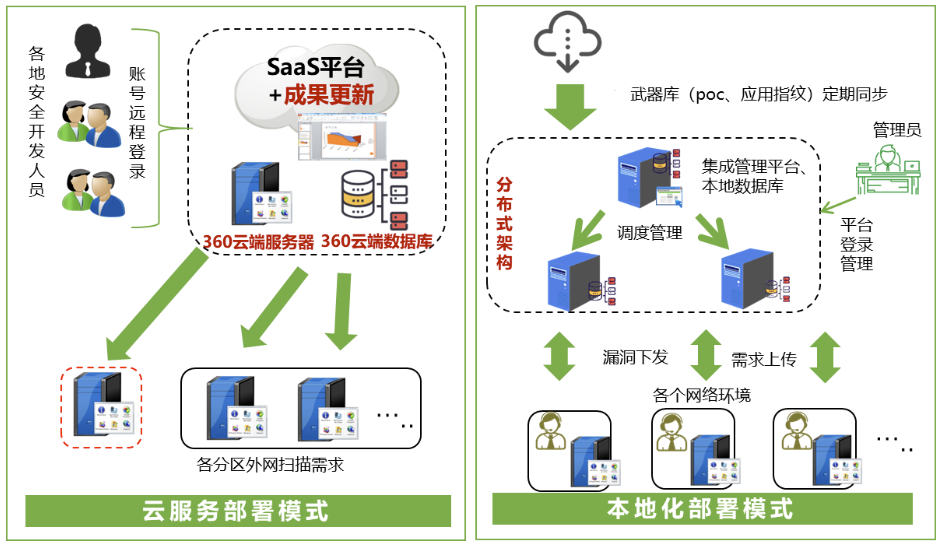
These assets are relatively controllable, and after long-term operation and management, each unit has already obtained relatively complete asset information. To further improve the internal network asset list and update it incrementally at any time, an internal network asset scanning and detection tool can be used to assist the user unit in completing this task.
(2) Analysis of Network Architecture and Security Strategies
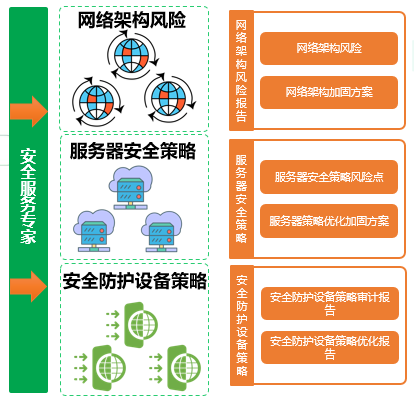
Whether an attack on an important target system of a certain unit can succeed depends on whether the current network architecture of that unit is scientific and whether the security strategies are targeted.
The network architecture should be multi-layered, the protection measures should be diversified, and important systems should have sufficient resilience and redundancy capabilities. Based on the network topology diagram of the target unit and the configuration operation manuals of related systems, assign security experts to conduct a comprehensive assessment of the existing network architecture and security policy system, and issue an assessment report.
(3) System Security Assessment
- Internet penetration testing
Conduct penetration testing for the systems of user units that provide services over the Internet, such as portal websites, online customer service, external network emails, recruitment management, etc.
- Intranet penetration testing
Provide penetration testing for relevant systems within the internal network of the user unit, such as project management system, defect management system, risk control system, centralized big data platform, business operation management platform, IT service management system, and configuration management system, etc.
- System vulnerability scanning
Conduct vulnerability scans for all assets within the internal network of the user's organization: network devices, servers, office PCs, databases, virtual machines, web applications, security devices, etc.
- System configuration verification
Firstly, conduct security configuration checks on the important target assets of the user units, such as business systems, servers, databases, network devices, and security equipment. Through a certain period of sorting out, further extend the scope to all the information assets of the entire unit, and gradually establish the baseline standards for asset security configuration of this unit.
- System code audit
Conduct source code auditing for the important target systems specified by the user units. Use auditing tools to identify security risks at the coding level. Based on the professional experience of the technical service personnel, conduct manual auditing and verification of business logic issues hidden in the code, such as authentication and payment transactions, for important functions.
- APP Security Testing
We provide comprehensive security testing for important APP applications related to user units, including WeChat official accounts, WeChat mini-programs, transaction-related, business district-related, and community-related ones, covering client-side, server-side, and the entire network communication process.
- Security retest
Through the first security testing process, the identified security issues in the system were sorted out, and detailed confirmation and communication were conducted with the relevant departments and responsible persons of the user unit. The security assessment report was compiled, and the problems that required security reinforcement were comprehensively rectified. Then, a second regression test was carried out for these issues to verify whether the reinforcement work was successful, and the final security assessment report was provided.
Scheme value
Comply with the requirements for information system security assessment stipulated in national-level protection regulations, security laws, regulations on the protection of critical information infrastructure, and relevant industry policies.
Emphasize both architecture and strategy, combine tools with manual work, and focus on the overall effect.
Have security assessment measures covering the entire life cycle of the system, providing overall guarantee capabilities
Comprehensively narrow down system security risks and hazards, and provide one-stop security assessment services.
Our successful case studies
Our Company's Case
OceanView's Private Cloud Security Solution
Our Company's Case
Construction of Data Protection Platform for Binzhou People's Hospital
Our Company's Case